1. What is the projected Compound Annual Growth Rate (CAGR) of the Information Security Risk Assessment?
The projected CAGR is approximately XX%.
 Information Security Risk Assessment
Information Security Risk AssessmentInformation Security Risk Assessment by Type (Technical Assessment, Personnel Assessment, Other), by Application (Financial Industry, Telecommunications Industry, Education Industry, Medical Industry, Municipal, Others), by North America (United States, Canada, Mexico), by South America (Brazil, Argentina, Rest of South America), by Europe (United Kingdom, Germany, France, Italy, Spain, Russia, Benelux, Nordics, Rest of Europe), by Middle East & Africa (Turkey, Israel, GCC, North Africa, South Africa, Rest of Middle East & Africa), by Asia Pacific (China, India, Japan, South Korea, ASEAN, Oceania, Rest of Asia Pacific) Forecast 2026-2034
MR Forecast provides premium market intelligence on deep technologies that can cause a high level of disruption in the market within the next few years. When it comes to doing market viability analyses for technologies at very early phases of development, MR Forecast is second to none. What sets us apart is our set of market estimates based on secondary research data, which in turn gets validated through primary research by key companies in the target market and other stakeholders. It only covers technologies pertaining to Healthcare, IT, big data analysis, block chain technology, Artificial Intelligence (AI), Machine Learning (ML), Internet of Things (IoT), Energy & Power, Automobile, Agriculture, Electronics, Chemical & Materials, Machinery & Equipment's, Consumer Goods, and many others at MR Forecast. Market: The market section introduces the industry to readers, including an overview, business dynamics, competitive benchmarking, and firms' profiles. This enables readers to make decisions on market entry, expansion, and exit in certain nations, regions, or worldwide. Application: We give painstaking attention to the study of every product and technology, along with its use case and user categories, under our research solutions. From here on, the process delivers accurate market estimates and forecasts apart from the best and most meaningful insights.
Products generically come under this phrase and may imply any number of goods, components, materials, technology, or any combination thereof. Any business that wants to push an innovative agenda needs data on product definitions, pricing analysis, benchmarking and roadmaps on technology, demand analysis, and patents. Our research papers contain all that and much more in a depth that makes them incredibly actionable. Products broadly encompass a wide range of goods, components, materials, technologies, or any combination thereof. For businesses aiming to advance an innovative agenda, access to comprehensive data on product definitions, pricing analysis, benchmarking, technological roadmaps, demand analysis, and patents is essential. Our research papers provide in-depth insights into these areas and more, equipping organizations with actionable information that can drive strategic decision-making and enhance competitive positioning in the market.
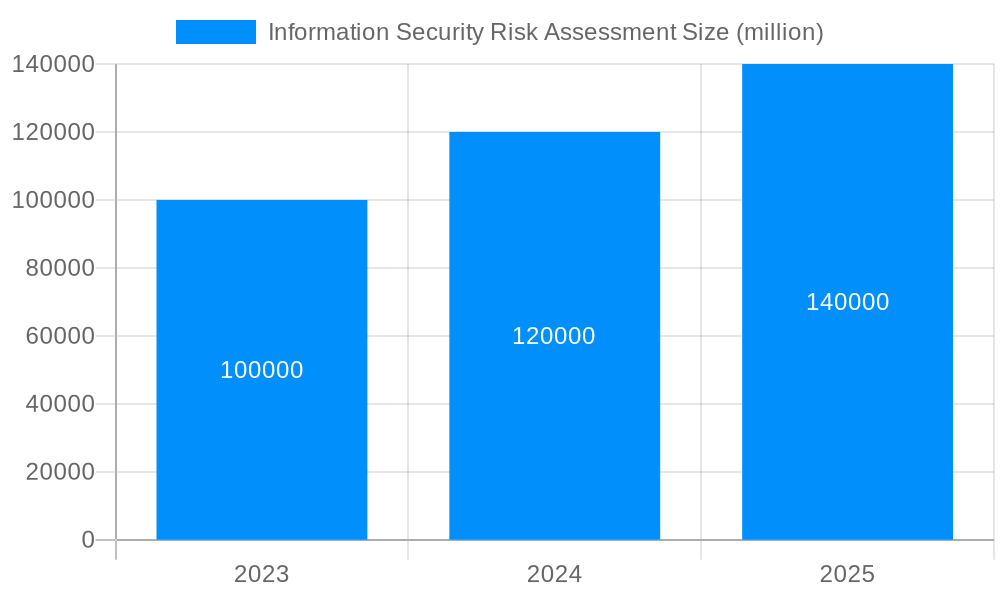
The market for Information Security Risk Assessment (ISRA) has experienced robust growth in recent years, with a global market size valued at millions in 2025. Driven by increasing cybersecurity threats and regulatory compliance requirements, the market is anticipated to exhibit a CAGR of XX% during the forecast period (2025-2033). Key market drivers include the growing adoption of cloud computing, the proliferation of IoT devices, and the increasing sophistication of cyberattacks. The demand for ISRA services is particularly strong in sectors such as financial services, telecommunications, healthcare, and government.
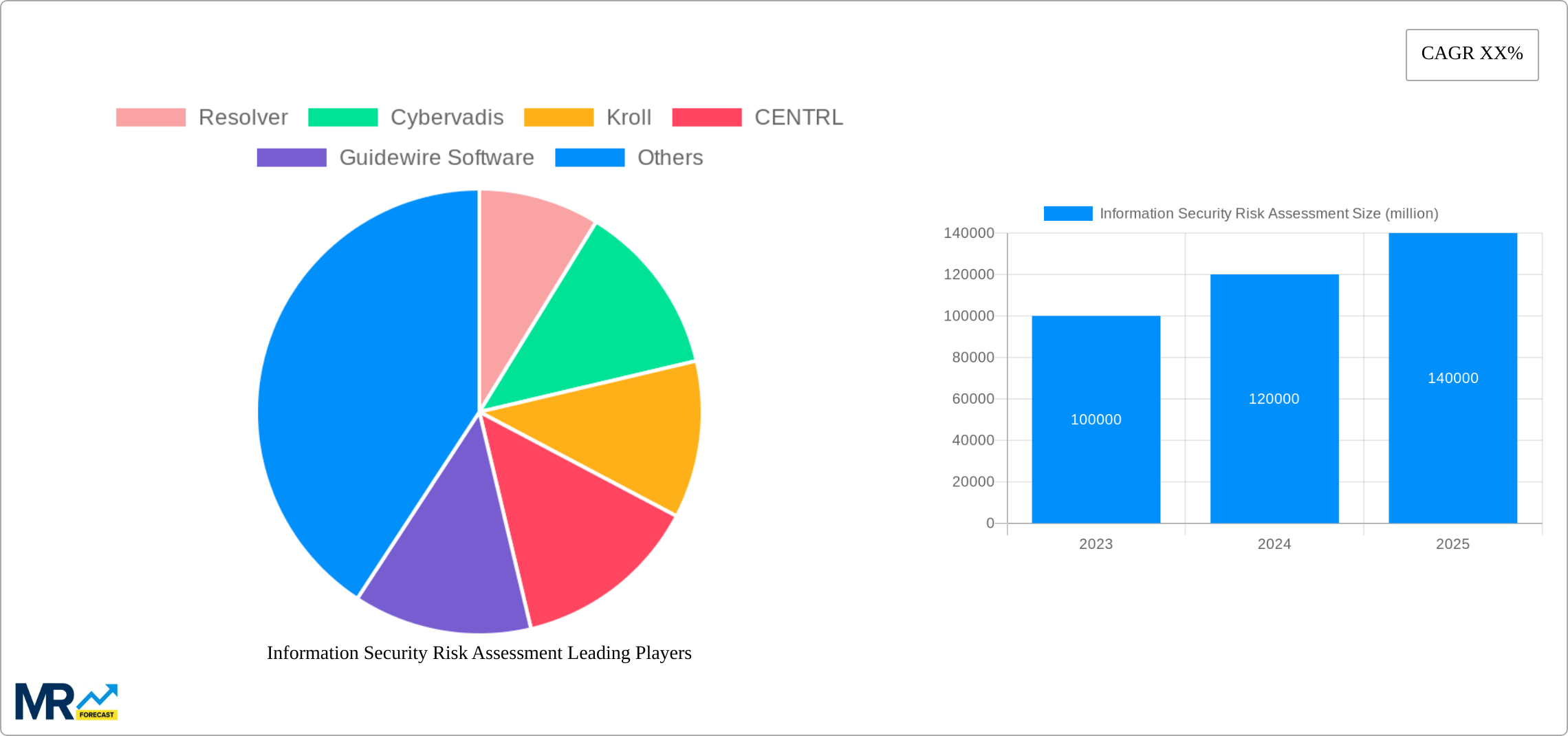

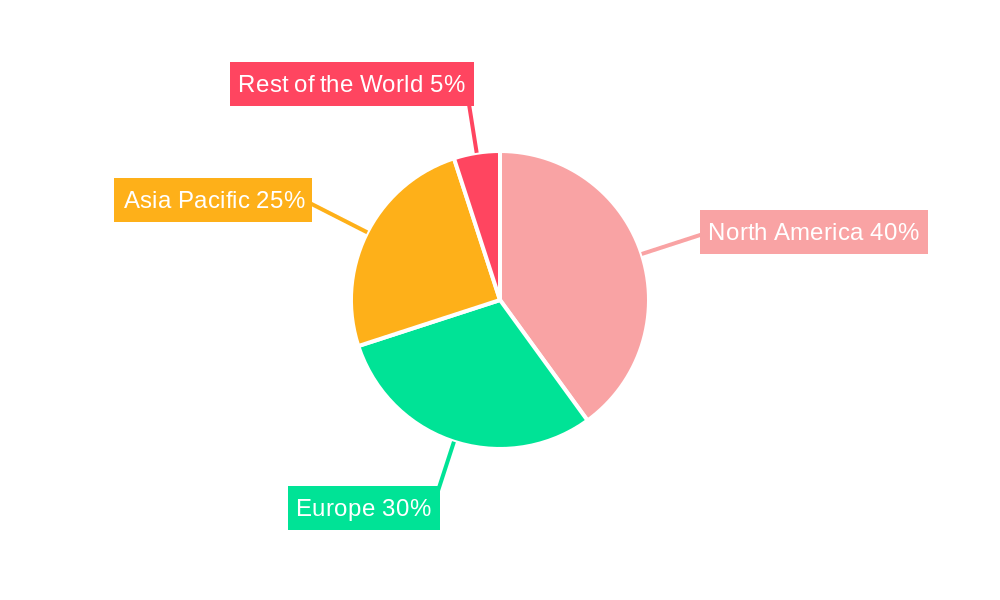
The ISRA market is segmented by type (Technical Assessment, Personnel Assessment, Other), application (Financial Industry, Telecommunications Industry, Education Industry, Medical Industry, Municipal, Others), and region (North America, South America, Europe, Middle East & Africa, Asia Pacific). Prominent companies operating in this market include Resolver, Kroll, Guidewire Software, MetricStream, SecurityScorecard, and Synoptek, among others. The competitive landscape is characterized by a diverse range of vendors offering specialized solutions tailored to meet the unique requirements of various industries.

The information security risk assessment market is experiencing significant growth due to rising concerns about cyber threats and data breaches. The increasing adoption of cloud computing, the Internet of Things (IoT), and mobile computing has expanded the attack surface for organizations. This has led to a rise in cyberattacks targeting critical infrastructure, financial institutions, and healthcare organizations. The market is further driven by regulatory compliance requirements, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), which mandate organizations to implement robust security measures to protect personal data.
Increasing Cyber Threats: The growing sophistication and frequency of cyberattacks are forcing organizations to reassess theirセキュリティ対策. Risk assessments help identify potential vulnerabilities and prioritize remediation efforts to mitigate the impact of cyber incidents.
Regulatory Compliance: Stringent data protection regulations are compelling organizations to implement comprehensive security measures. Risk assessments are an essential component of compliance frameworks, demonstrating an organization's commitment to data security and reducing the risk of fines and penalties.
Cloud Adoption: The rapid adoption of cloud computing has introduced new security challenges. Cloud providers share responsibility for securing the infrastructure, while organizations remain responsible for securing their applications and data. Risk assessments help organizations understand their cloud security posture and allocate resources accordingly.
Skilled Workforce Shortage: The persistent and often critical shortage of highly skilled cybersecurity professionals remains a significant hurdle for organizations undertaking risk assessments. Conducting thorough and effective risk assessments demands deep expertise across a spectrum of security tools, advanced analytical techniques, and a nuanced understanding of evolving industry best practices. This talent gap can lead to incomplete assessments, overlooking critical vulnerabilities.
Complexity of IT Environments: Modern and rapidly evolving IT environments are characterized by intricate interdependencies between systems, applications, cloud services, and a proliferating array of connected devices. The sheer complexity of these interconnected ecosystems makes a comprehensive risk assessment a time-consuming and resource-intensive undertaking, requiring specialized knowledge to map, analyze, and prioritize potential threats across diverse technological landscapes.
Budget Constraints: Many organizations grapple with stringent budget limitations, which can significantly restrict their capacity to invest in robust and comprehensive risk assessment processes. Insufficient investment can result in the adoption of superficial assessments, the underutilization of advanced tools, and the implementation of inadequate security measures, thereby increasing an organization's vulnerability to sophisticated cyber threats.
North America is expected to dominate the market, driven by increasing regulatory compliance requirements and the presence of major technology companies.
Financial Industry: The financial industry faces significant cyber threats due to the large amounts of sensitive data it handles. Risk assessments are crucial for protecting financial institutions from data breaches and fraud.
Healthcare Industry: The healthcare industry faces unique security challenges related to patient data privacy and the interconnectedness of medical devices. Risk assessments help healthcare providers identify and mitigate potential threats.
Artificial Intelligence (AI) and Machine Learning (ML): The integration of AI and ML technologies is fundamentally reshaping the landscape of risk assessment. These advanced capabilities are instrumental in automating the identification of vulnerabilities, refining threat analysis through predictive modeling, and enabling more intelligent and dynamic prioritization of risks. This automation significantly enhances the efficiency, accuracy, and overall effectiveness of risk management processes, allowing for proactive threat detection and response.
Cloud-Based Risk Assessment Tools: The proliferation of cloud-based risk assessment solutions offers organizations highly flexible, scalable, and often more cost-effective alternatives for conducting risk analyses, including those performed remotely. These platforms leverage advanced functionalities such as automated vulnerability scanning, continuous threat intelligence feeds, and sophisticated reporting mechanisms, democratizing access to powerful risk assessment capabilities.
Integration with Security Information and Event Management (SIEM) Systems: A key development is the increasing integration of dedicated risk assessment tools with SIEM systems. This synergy provides a unified and holistic view of an organization's security posture by correlating risk findings with real-time security events, enabling a more contextualized understanding of threats and a faster response to incidents.
Adoption of Continuous Monitoring: The shift towards adopting continuous monitoring solutions represents a proactive evolution in risk management. By enabling the real-time tracking of security threats, vulnerabilities, and system changes, these solutions empower organizations to identify and address risks as they emerge, fostering a more agile and resilient security framework for preemptive risk mitigation.
A comprehensive Information Security Risk Assessment report serves as an indispensable resource, delivering an in-depth and multifaceted analysis of the industry. This includes an examination of prevailing trends, critical growth drivers, significant challenges and restraints, detailed segmentation of market areas, and an overview of leading industry players. Such reports offer invaluable, actionable insights for organizations striving to fortify their security posture, effectively mitigate evolving cyber threats, and make informed strategic decisions in the dynamic information security landscape.

| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of XX% from 2020-2034 |
| Segmentation |
|
Note*: In applicable scenarios
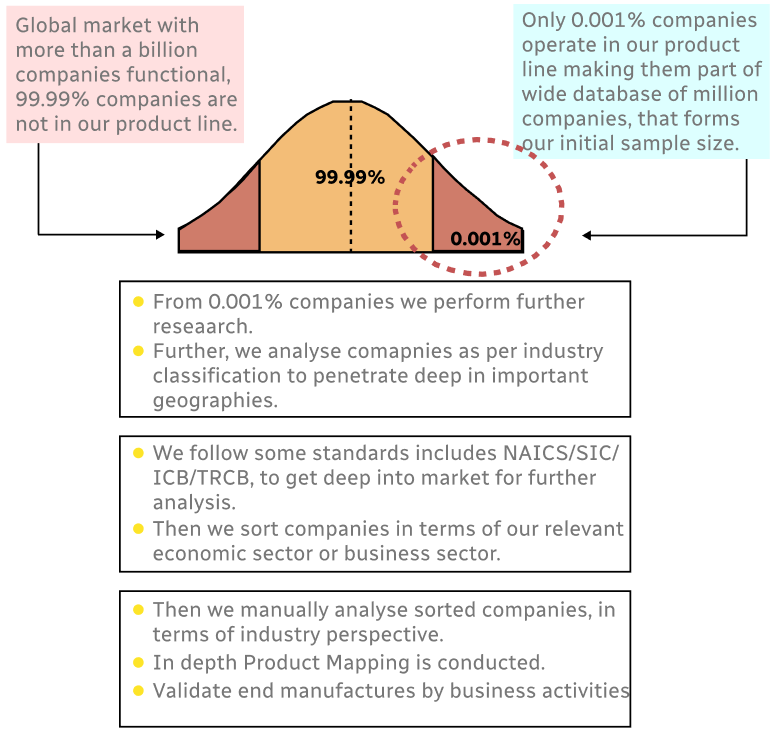
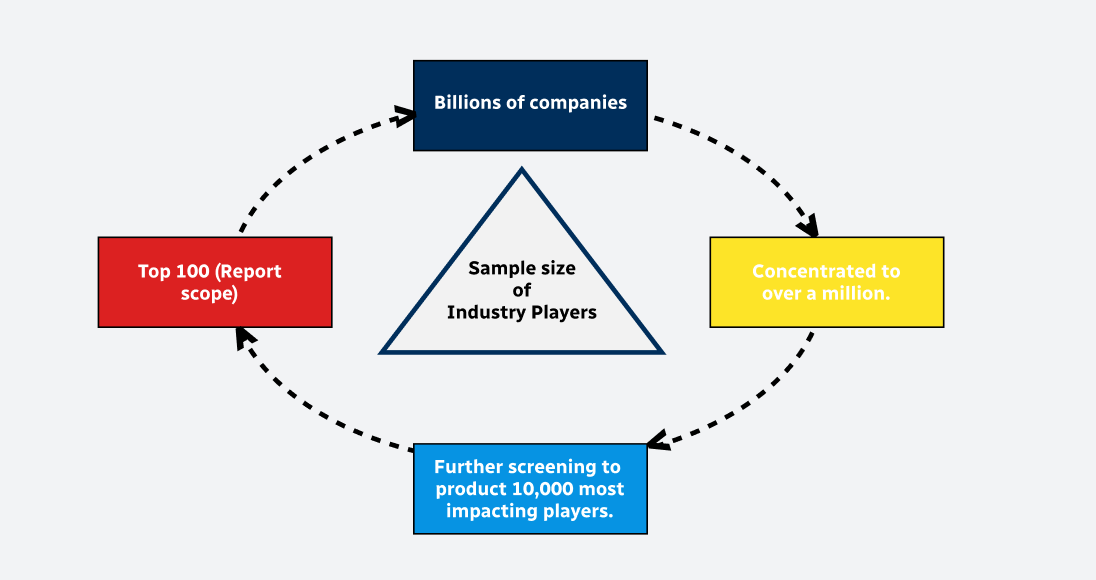
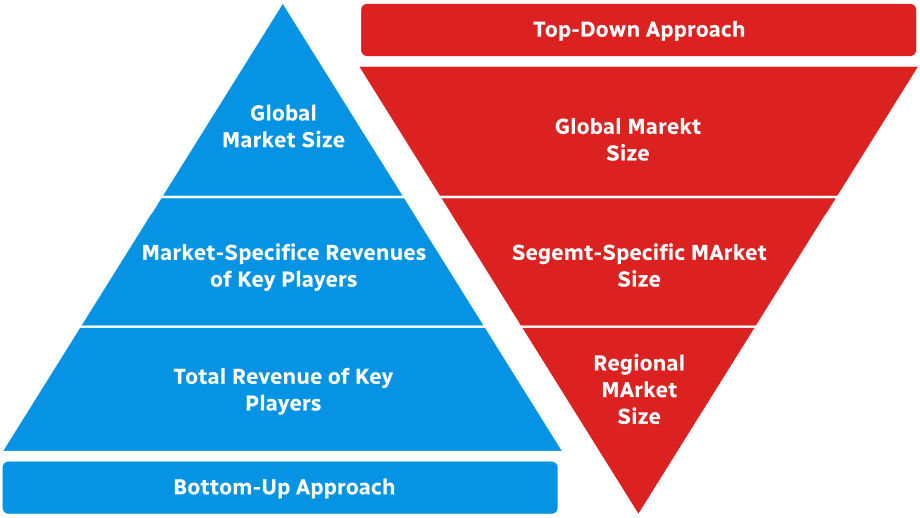
Primary Research
Secondary Research
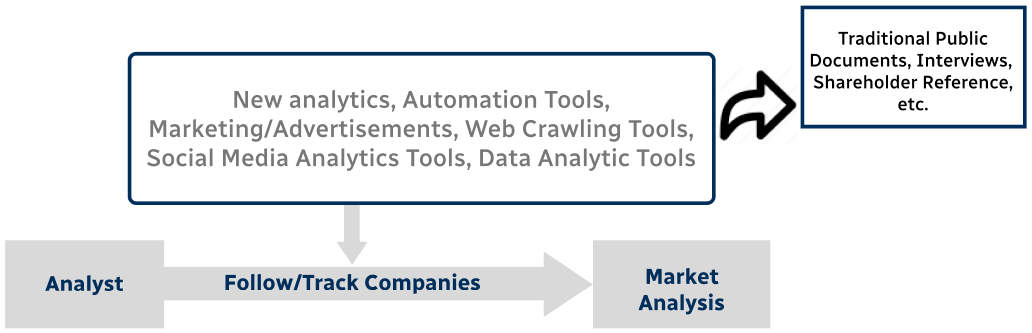
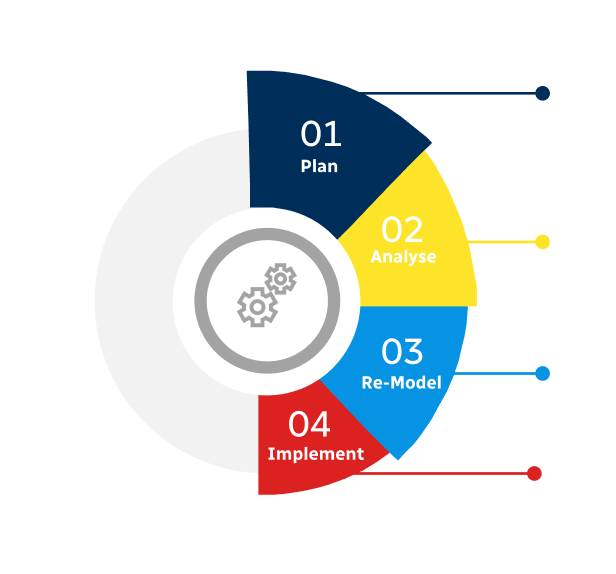
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence
The projected CAGR is approximately XX%.
Key companies in the market include Resolver, Cybervadis, Kroll, CENTRL, Guidewire Software, Corax, Ncontract, Menaya, Black Kite, MetricStream, SBS CyberSecurity, SecurityScorecard, Sectara, OCHIN, SailPoint Technologies, Synoptek, CyberSecOp, TestPros.
The market segments include Type, Application.
The market size is estimated to be USD XXX million as of 2022.
N/A
N/A
N/A
N/A
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 3480.00, USD 5220.00, and USD 6960.00 respectively.
The market size is provided in terms of value, measured in million.
Yes, the market keyword associated with the report is "Information Security Risk Assessment," which aids in identifying and referencing the specific market segment covered.
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
To stay informed about further developments, trends, and reports in the Information Security Risk Assessment, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.